PDF Signature Verification What Developers Need to Know
Most developers encounter signed PDFs without knowing what the cryptographic signature actually guarantees. Here is what you need to know to pdf signature check verify correctly.
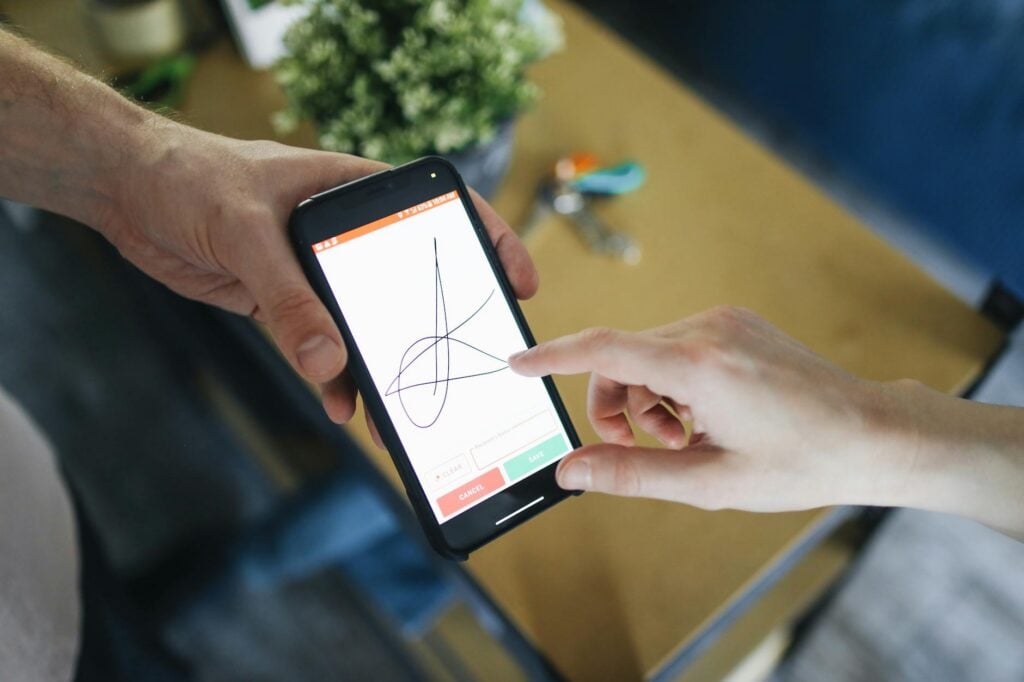
Most developers have worked with signed PDFs — a signed contract, a certified bank statement, a government form. But “signed” means different things depending on who you ask. The visual scrawl in the signature box and the cryptographic signature embedded in the file are two entirely different things. Only one of them actually guarantees anything.
This guide covers how PDF digital signatures work, what the different validity states mean, and how to verify them programmatically.
The Signature You See vs. the Signature That Matters
When someone “signs” a PDF with a drawing tool or image stamp, they are placing a picture of a signature on the page. It looks official but carries no security guarantee. Anyone can copy that image to another document.
A digital signature is different. It is a cryptographic artifact embedded in the PDF structure itself — separate from any visual element. When a document is digitally signed:
- A hash of the document content is computed.
- That hash is encrypted with the signer’s private key.
- The encrypted hash (the signature) is stored in the PDF along with the signer’s certificate chain.
When you verify the signature, you decrypt it using the public key from the certificate, recompute the hash from the current document content, and compare. If they match, the document has not been modified since signing. If they do not match — or the certificate is not trusted — the signature is invalid.
The Four Signature Validity States
Not every digital signature is equal. When you pdf signature check verify, you will encounter one of four states:
| Signature State | What It Means | What to Do |
|---|---|---|
| Valide | Hash matches, certificate chain is trusted, certificate was active at signing time | Trust the signature — verify the signer identity against your expected certificate |
| Invalid | Document content changed after signing, or signature data is corrupt | Reject the document; it has been tampered with or is malformed |
| Unknown | Signature structure is intact, but the certificate cannot be verified (untrusted root, missing OCSP, etc.) | Cannot trust the signature — request a re-signed document or obtain the trusted root certificate |
| Revoked | Certificate was valid at issuance but later revoked by the CA (e.g. key compromise) | Reject unless LTV data proves the certificate was valid before revocation |
The “Unknown” state trips up most developers. A structurally correct signature with a self-signed or enterprise-internal certificate shows as Unknown in most tools because those tools cannot reach the issuer. For internal document workflows, you may explicitly trust that root; for documents from external parties, Unknown is not acceptable.
Long-Term Validation (LTV): Why Timestamps Matter
Certificates expire. If someone signed a document five years ago and their certificate has since expired, does the signature still hold?
It depends on Long-Term Validation (LTV). When LTV is embedded, the PDF contains:
- A trusted timestamp from a timestamp authority (TSA)
- OCSP responses or CRL data confirming the certificate status at signing time
With LTV, you can prove the certificate was valid when the signature was applied — even after expiry. Without it, you can only verify the signature against the current certificate status, which becomes impossible once the certificate expires or the OCSP responder is decommissioned.
For contracts or regulated documents with long retention requirements (7+ years in many jurisdictions), LTV is not optional. Always check for it when building signature verification workflows.
Verifying PDF Signatures Programmatically
Using Python with pypdf
Le pypdf library provides access to PDF signature fields and their underlying metadata. Here is a minimal example to check whether a PDF has digital signatures and read their state:
import sys
from pypdf import PdfReader
def check_pdf_signatures(path: str) -> None:
reader = PdfReader(path)
sig_fields = [
name for name, field in (reader.get_fields() or {}).items()
if field.get("/FT") == "/Sig"
]
if not sig_fields:
print("No digital signature fields found.")
return
print(f"Found {len(sig_fields)} signature field(s):")
for name in sig_fields:
sig_obj = reader.get_fields()[name]
sig_dict = sig_obj.get("/V")
if not sig_dict:
print(f" {name}: field present but unsigned")
continue
signer_name = sig_dict.get("/Name", "Unknown")
signing_time = sig_dict.get("/M", "No timestamp")
reason = sig_dict.get("/Reason", "")
location = sig_dict.get("/Location", "")
print(f" {name}:")
print(f" Signer: {signer_name}")
print(f" Time: {signing_time}")
if reason:
print(f" Reason: {reason}")
if location:
print(f" Location: {location}")
if __name__ == "__main__":
check_pdf_signatures(sys.argv[1])This reads signature metadata directly from the PDF structure. For full cryptographic verification — confirming the hash and validating the certificate chain — use pyhanko ou endesive, both of which wrap the PKCS#7 verification layer.
Using qpdf on the Command Line
For quick inspection from the command line without a Python environment:
# Show encryption and signature info
qpdf --show-encryption input.pdf
# Full JSON output with signature details
qpdf --json input.pdf | python3 -m json.tool | grep -A 20 '"sig"'qpdf is useful in CI pipelines or shell scripts where setting up a Python virtualenv adds unnecessary overhead.
Common Verification Scenarios
Signed contracts from clients — Check both the validity state and the certificate issuer. A valid signature from an untrusted root (self-signed cert) provides no external assurance. You are trusting whoever generated the key.
Government and regulatory documents — These typically use nationally trusted certificate authorities. Verify that the certificate chain anchors to the expected root CA, not just that the signature reads as “valid.”
Bank statements and invoices — Many are batch-signed using document signing certificates issued to an organization. The signer name will reflect the institution, not an individual employee.
Verify Without Writing Code
If you need to quickly pdf signature check verify a file without setting up a development environment, the IO Tools PDF Signature Checker lets you upload a file and see signature details instantly — useful for one-off verification or for testing sample files before building a production pipeline.
Installez nos extensions
Ajoutez des outils IO à votre navigateur préféré pour un accès instantané et une recherche plus rapide
恵 Le Tableau de Bord Est Arrivé !
Tableau de Bord est une façon amusante de suivre vos jeux, toutes les données sont stockées dans votre navigateur. D'autres fonctionnalités arrivent bientôt !
Outils essentiels
Tout voir Nouveautés
Tout voirMise à jour: Notre dernier outil was added on Mai 10, 2026